
The data supplied on this web site doesn’t, and isn’t supposed to, act as authorized, monetary or credit score recommendation. See Lexington Regulation’s editorial disclosure for extra info.
After you’ve been notified of a knowledge breach, you need to contact your financial institution and the three main credit score bureaus as quickly as doable.
When a knowledge breach happens, you need to monitor all your accounts for suspicious exercise. Creating alerts in your banking accounts may also help you react to suspicious transactions. An analogous technique is suggested in your credit score report; in sure circumstances, firms must present credit score monitoring companies to their clients for as much as 12 months.
Information breaches can result in adverse conditions, akin to id theft and bank card fraud. Beneath, we’ll talk about what to do after a knowledge breach happens and discover choices for dependable credit score monitoring companies.
Key takeaways:
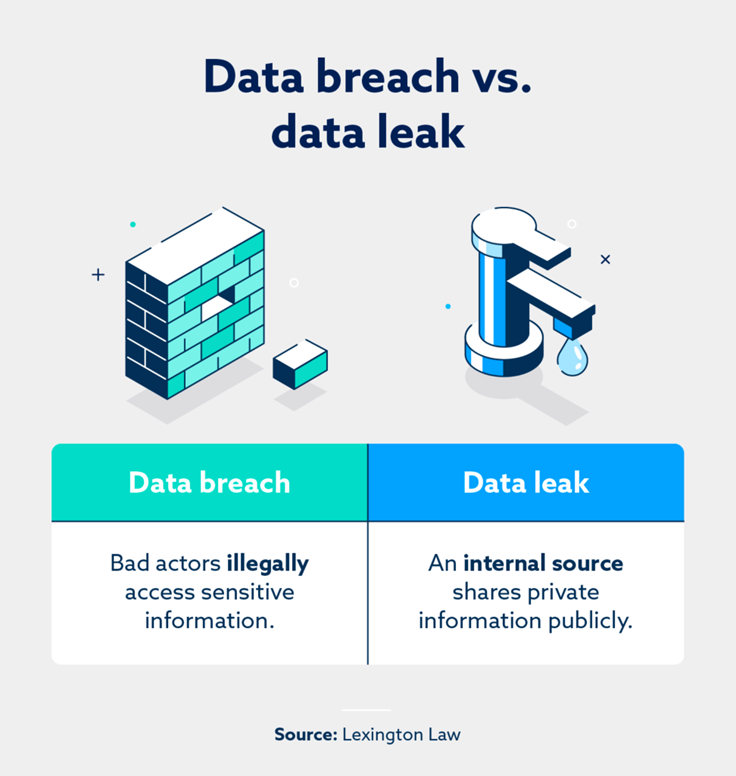
- An information breach happens when cybercriminals illegally achieve entry to delicate info.
- In sure circumstances, firms shall be ordered to supply credit score monitoring companies to their clients for as much as 12 months.
- The Equifax® information breach of 2017 compromised 148 million Individuals and 15 million British residents.
Desk of contents:
What’s a knowledge breach?
An information breach happens when cybercriminals and unhealthy actors illegally entry delicate information. An information breach can occur to particular people and huge organizations—such because the 2017 Equifax information breach, which impacted practically 150 million Individuals and 15 million British residents.
If a company is held accountable for a knowledge breach by a court docket of legislation, compensation could also be issued to victims. For instance, the Equifax breach settlement was finalized in January 2022 and resulted in free credit score monitoring companies and as much as $425 million of assist to impacted people.
How do you test in case your private info was uncovered?
The Information Breach Notification Act gives pointers and rules within the occasion of a knowledge breach. Part 2 of this act states that companies and federal companies should inform affected people that their information has been leaked “with out unreasonable delay.”
These particular pointers are related after a knowledge breach happens. Listed here are a number of actionable steps if you wish to take proactive measures to fight a knowledge breach:
- Intrusion detection system (IDS): This know-how can monitor a community and decide if suspicious or malicious exercise is underway.
- Information leak checker web sites: Web sites like Have I Been Pwnd will aid you test if considered one of your emails was a part of a knowledge breach.
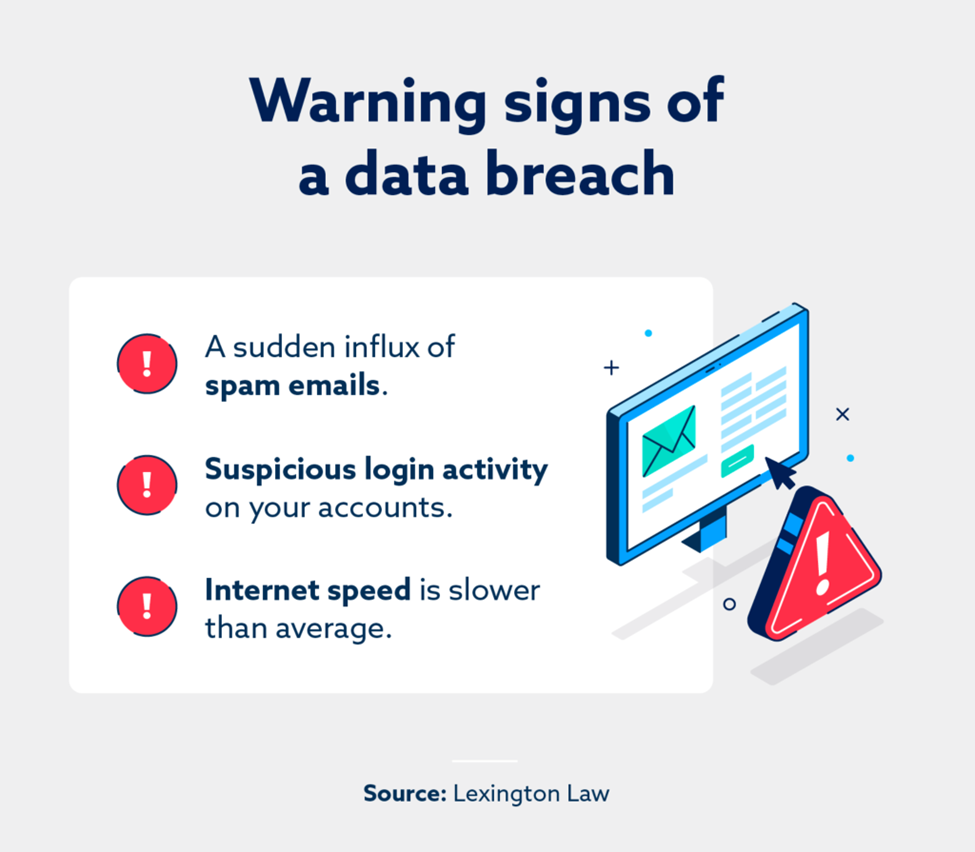
- Assessment your emails: In case your spam and junk e mail containers have an uncommon quantity of spam, your e mail may’ve been compromised.
What must you do after a knowledge breach?
After you’ve obtained a discover that your information was compromised, it’s pure to really feel overwhelmed or upset by this violation of your privateness. However, taking motion and making changes is one of the best ways to attenuate or stop the worst outcomes.
Change your passwords
Should you had been a part of a knowledge breach, there’s a excessive chance that cybercriminals may possess your present login info. Altering your passwords can stop unhealthy actors from signing into your accounts.
Ideally, it’s finest to make use of a posh password comprising higher and lowercase letters, particular characters and numbers. The much less this new password resembles your previous one, the higher. Moreover, altering your password each few months is a wonderful safety measure.
Activate two-factor authentication (2FA)
Two-factor authentication (2FA) is an extra login step the place customers have to complete signing in on a trusted machine, often a smartphone. 2FA reduces the chance of a nasty actor illegally accessing considered one of your accounts as the extra login measure (your cellphone) is in your particular person.
Look into credit score monitoring companies
For these questioning what credit score monitoring is, the time period refers to any service that watches your credit score reviews and alerts you about suspicious exercise that doesn’t match your traditional monetary habits.
Credit score monitoring companies search for the whole lot from fluctuations in your credit score rating to new accounts which have been opened in your identify. Lex OnTrack is a monitoring service that tracks your credit score historical past and helps shield your id from fraud.
Freeze your credit score with the three credit score bureaus
Studying freeze your credit score may also help you cease cybercriminals from taking unauthorized actions along with your credit score. To completely freeze your credit score, you’ll at the very least need to contact Equifax®, Experian® and TransUnion®—the three main credit score bureaus.
Contact your financial institution
Talking along with your financial institution after you’ve been notified of a knowledge breach is an efficient solution to shield your funds. You’ll have a possibility to inform your monetary establishment of this unlucky occasion, and also you’ll additionally be capable of evaluate current account exercise.
If current purchases had been made in your account that don’t align along with your habits, they could possibly be tied to illegal exercise.
What states have information breach legal guidelines?

Each state in America has cybersecurity legal guidelines that shield civilians, organizations and federal companies within the occasion of a knowledge breach. The Information Breach Notification Act usually applies to all 50 states alongside territories and districts.
On the time of writing, California, Colorado, Connecticut, Utah and Virginia have distinctive information privateness legal guidelines that differ considerably from their contemporaries. As an example, the California Shopper Privateness Act (CCPA) offers Californians the best to demand all info that an organization and its third-party companions have on them.
3 causes information breaches occur
Information breaches are extremely alarming, and it’s tempting to seek for a simple clarification as to why they occur. Although solely a small variety of them are profitable, cyberattacks are fairly widespread.
A examine by the Clack Faculty discovered that some computer systems could also be attacked, on common, roughly 2,200 instances every day. Some elements that elevate the percentages of a cyberattack succeeding are outlined beneath.
1. Malware assaults
Malware (or malicious software program) can compromise safety if somebody downloads it onto their machine. For instance, a key logger is a sort of malware that information each keystroke a person inputs. Such software program may assist cybercriminals steal admin credentials from a company, then log in and entry delicate information.
2. Inside information leak
“What’s a knowledge leak?” is a good query, as this time period sounds comparable to a knowledge breach. Nevertheless, a knowledge leak happens when an inner supply releases non-public info to most people. If somebody working at a company offers out confidential login particulars, a cybercriminal may capitalize on that and provoke a knowledge breach.
3. Outdated software program
Software program updates bolster a community’s safety and make it more durable for hackers to slide previous defenses. Repeated cyberattacks which are launched in opposition to methods with outdated software program are extra doubtless to achieve success.
Monitor your credit score with Lexington Regulation Agency
The sheer variety of cyberattacks that happen every day will be alarming, however there are various methods to guard your self from digital disturbances. A credit score monitoring service is a wonderful device that works within the background and catches seemingly minute particulars.
Discover Lexington Regulation’s companies, which embrace credit score monitoring in addition to help with difficult errors on credit score reviews, if any are discovered.
Notice: Articles have solely been reviewed by the indicated legal professional, not written by them. The data supplied on this web site doesn’t, and isn’t supposed to, act as authorized, monetary or credit score recommendation; as an alternative, it’s for basic informational functions solely. Use of, and entry to, this web site or any of the hyperlinks or assets contained throughout the website don’t create an attorney-client or fiduciary relationship between the reader, person, or browser and web site proprietor, authors, reviewers, contributors, contributing corporations, or their respective brokers or employers.


